The Biggest Problems Caused by Ransomware
(And How to Protect Your Business)
1. Introduction: The Rising Threat of Ransomware in the Digital Age
Ransomware isn’t just a cybercrime buzzword anymore—it’s one of the most dangerous and costly threats businesses face today. With 85% of companies encountering at least one attack annually and many experiencing multiple breaches, ransomware is a persistent crisis. Beyond just encrypting data, modern ransomware operations include data theft, extortion, and long-lasting operational paralysis. And with traditional cybersecurity tools often falling short, it’s no longer a question of “if” but “when” an attack will happen. Understanding the full range of problems ransomware causes is the first step toward creating a truly resilient defense.
2. Financial Devastation from Ransomware Attacks
2.1 Ransom Demands and Payments
Hackers don’t just want attention—they want money. Ransom demands range from a few thousand to millions of dollars, depending on the target’s size and perceived value. While many organizations refuse to pay, a large portion feel forced to comply under pressure, especially if business continuity is at risk.
2.2 Remediation and Restoration Costs
Even if the ransom isn’t paid, the cleanup is costly. From hiring cybersecurity experts to restoring data and re-securing systems, the average remediation cost exceeds $4 million. This figure doesn’t include hidden expenses like rebranding, customer communications, or PR campaigns.
2.3 Lost Business and Revenue Opportunities
Every minute of downtime equals lost revenue. Retailers, manufacturers, healthcare providers, and financial services firms may be unable to operate for hours, days, or even weeks—crippling their ability to generate income.
2.4 Legal Fees, Fines, and Insurance Hikes
If sensitive data is breached, regulatory fines can stack up fast. Legal consultations, customer lawsuits, and skyrocketing cyber insurance premiums add even more financial burden post-incident.
3. Operational Disruptions That Paralyze Businesses
3.1 Downtime and Business Interruption
Systems frozen by ransomware can’t run business processes. That means halted production, failed transactions, and disconnected communication channels. The result? Chaos.
3.2 Data Loss and Corruption
Ransomware doesn’t just lock files—it often exfiltrates or corrupts them. Without recent, secured backups, data loss can be irreversible, especially in industries like healthcare, finance, or law where data is the lifeblood of operations.
3.3 Recovery Time and Resource Drain
On average, it takes 89 days to fully recover from an attack. IT teams are overwhelmed, normal operations are disrupted, and business as usual feels like a distant dream.
4. Reputational and Trust-Related Fallout
4.1 Customer Confidence and Brand Reputation
When customers learn their data was compromised, trust erodes. Competitors swoop in, customers churn, and it can take years (and a lot of money) to rebuild confidence.
4.2 Negative Publicity and Media Coverage
Ransomware attacks are headline grabbers. Media coverage often paints the victim as negligent or unprepared. Even loyal customers may begin to question your business practices.
5. Compliance, Legal, and Regulatory Pressures
5.1 Regulatory Fines and Penalties
Regulations like GDPR, HIPAA, and CCPA impose steep penalties for data breaches. Non-compliance not only results in fines but also tighter scrutiny from regulators.
5.2 Breach Notification Requirements
Organizations are legally obligated to notify affected parties and regulators after a breach. These disclosures can damage customer relations and public image.
5.3 Long-term Legal Exposure
Breach-related lawsuits from customers, partners, or shareholders can drag on for years. Each legal battle adds more cost and reputational strain.
6. Human and Psychological Toll of Ransomware
6.1 Employee Stress and IT Burnout
Employees may feel helpless, overworked, or even blamed. IT teams especially suffer burnout while handling crisis response, system restoration, and cybersecurity upgrades.
6.2 Customer Anxiety and Inconvenience
Disrupted services lead to unhappy customers. If their data is exposed, the stress—and potential legal action—only grows.
7. Strategic and Competitive Impact
7.1 Strategic Decision-Making in Crisis
Should a business pay the ransom or not? Either choice has consequences. Paying may encourage more attacks. Refusing could risk permanent data loss.
7.2 Exposure of Security Weaknesses
Successful attacks reveal critical vulnerabilities. Addressing them often requires restructuring IT departments, buying new software, and re-training staff.
7.3 Long-Term Competitive Disadvantage
In industries where uptime and trust are competitive advantages, a ransomware incident can set companies back for years—losing clients, investors, and momentum.
8. Why Legacy Solutions Are Failing to Stop Ransomware
Traditional firewalls, antivirus programs, and even some next-gen solutions lack ransomware-specific capabilities. They’re reactive, not proactive—detecting threats after damage is done. Ransomware now uses AI evasion, zero-day exploits, and fileless execution techniques that older tools can’t keep up with.
9. Key Characteristics of Modern Ransomware Attacks
Modern attacks follow a strategic sequence: infection → privilege escalation → data exfiltration → encryption. This “double extortion” ensures cybercriminals get paid, even if backups exist. Many rely on RaaS (Ransomware-as-a-Service) models, where attackers specialize in different stages, making them more effective and harder to trace.
10. Ransomware-as-a-Service: A Criminal Business Model
RaaS platforms function like SaaS businesses—with developers, support, affiliate commissions, and dashboards. This scalability increases attack volume and sophistication. Criminal groups no longer need deep technical skills—they just buy access and follow instructions.
11. Building Resilience: How Anti-Ransomware Solves These Problems
GBS’s solution goes beyond prevention—it builds cyber resilience. By combining pre-execution detection, behavior-based analytics, encryption key capture, and automated recovery, GBS minimizes downtime and ensures business continuity. It’s specifically built to counter modern ransomware tactics that bypass legacy defenses.
12. Conclusion: Shifting from Reaction to Prevention
Ransomware attacks are no longer isolated events—they’re a widespread epidemic. Businesses must shift from reactive strategies to proactive, resilience-based models. With a solution like GBS’s Anti-Ransomware, your organization can not only withstand attacks but also recover quickly and emerge stronger.
Here are a few FAQ that might help you understand our solution better –
13. FAQs About the Impact of Ransomware
13.1 What is the average cost of a ransomware attack?
Over $4 million, not including ransom payments, fines, or lost revenue.
13.2 How long does it take to recover from ransomware?
On average, about 89 days—but recovery time varies based on preparedness.
13.3 Why do businesses still pay the ransom?
Often because backups are insufficient or attackers exfiltrated sensitive data.
13.4 Are backups enough to protect against ransomware?
No. Many attackers steal data before encryption, rendering backups useless alone.
13.5 What are the most common ransomware entry points?
Phishing emails, unpatched software, open RDP ports, and misconfigured VPNs.
13.6 How does GBS’s Anti-Ransomware prevent attacks?
Through layered AI-driven detection, endpoint/network resiliency, and rapid recovery.
“Budget is tight.” “We already have antivirus.” The most dangerous cyber strategy? ✨ Assumptions.
Most breaches don’t happen from zero-day attacks… They happen because basic controls weren’t in place.
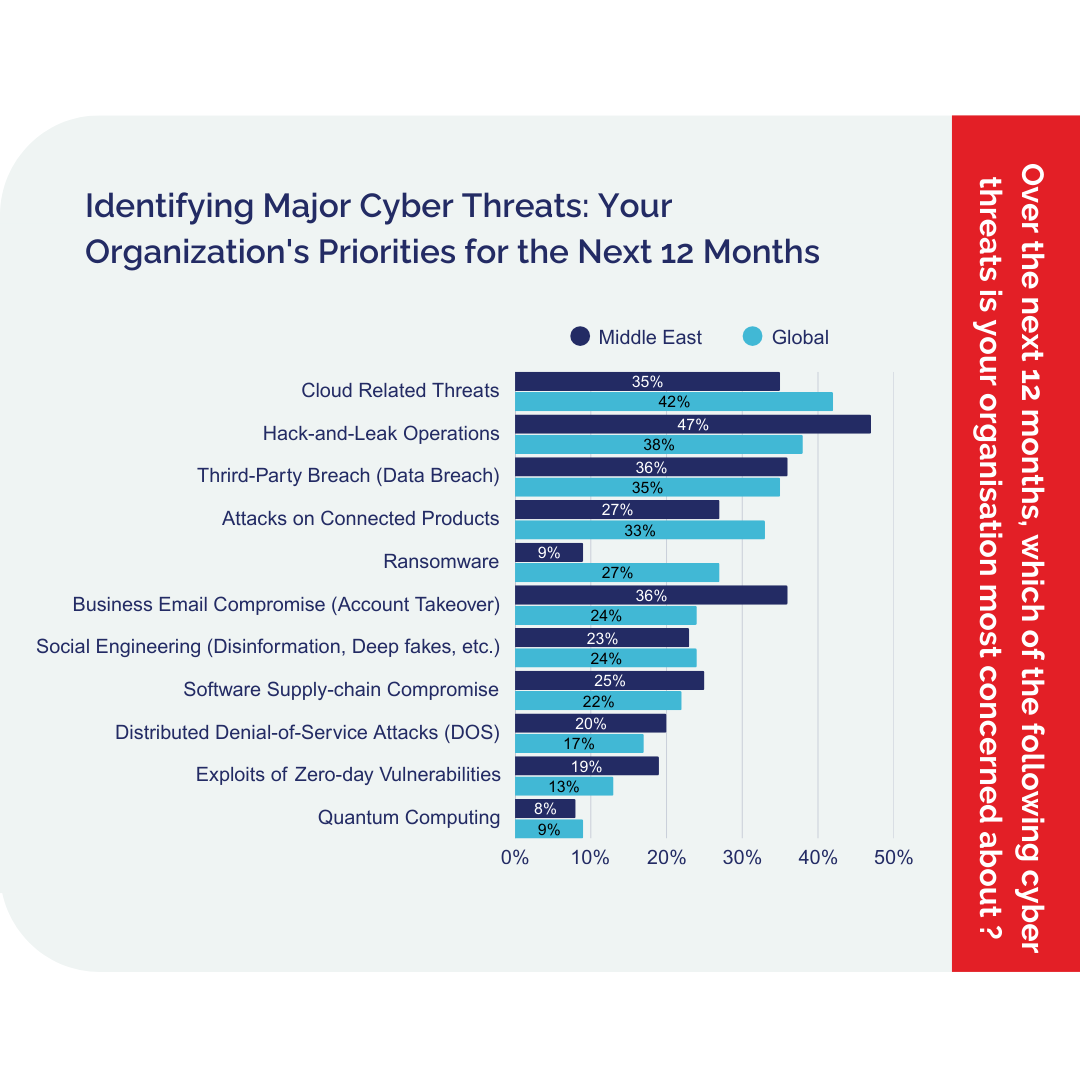
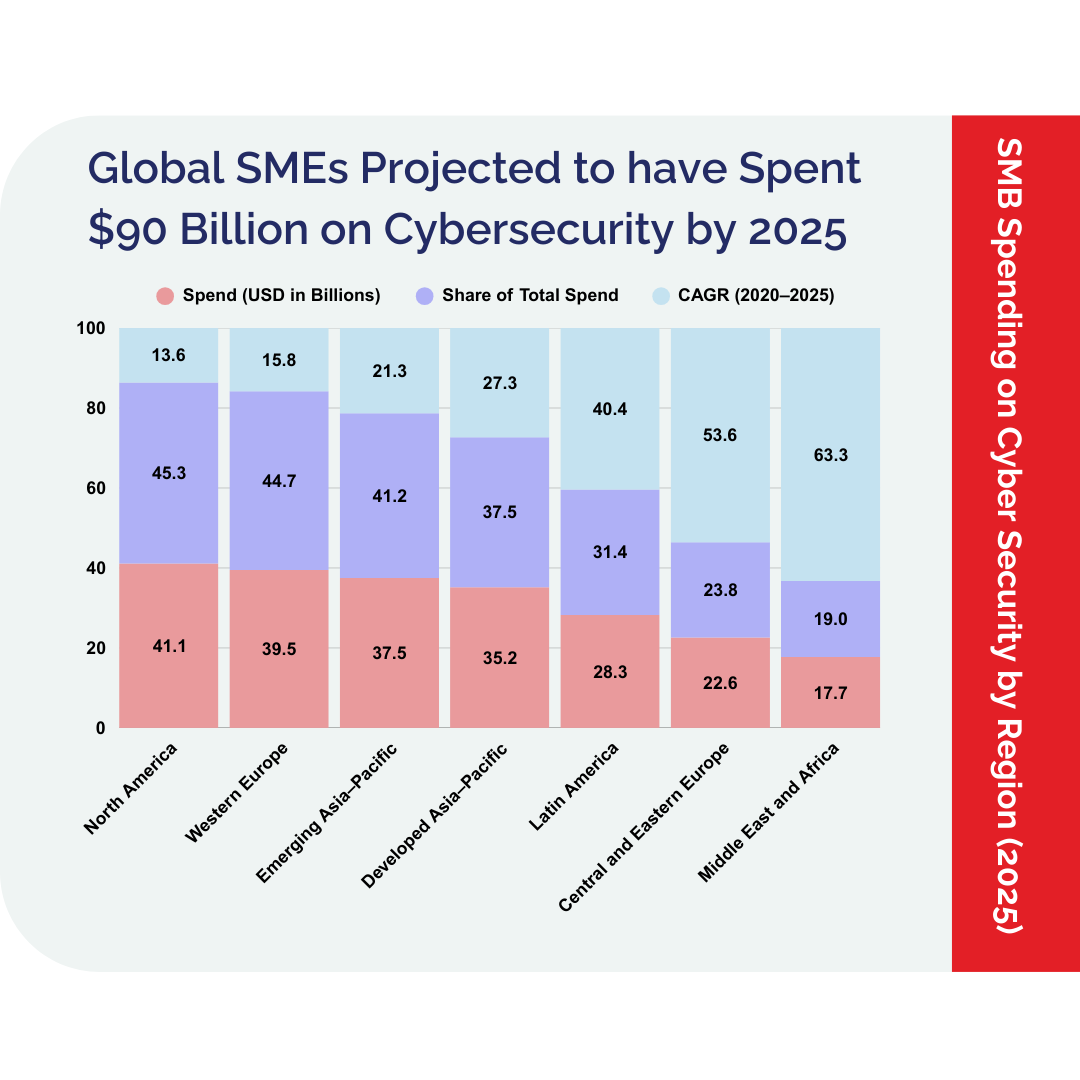
In our latest report, we unpack the simple, overlooked reasons UAE businesses are still vulnerable — and what real IT leaders are doing differently.
Backed by reports from Cisco, PwC, and our own analysis! Download the 2025 Cybersecurity Report
The State of
Cybersecurity in UAE
Download the 2025 Report Today,

Unlock Latest Cybersecurity Insights
Gain exclusive access to the State of Cybersecurity in the UAE – 2025 Report—your essential guide to navigating the evolving digital threat landscape.
Follow us on social media to stay updated on the latest developments – Facebook & LinkedIn
GBS has now released a UAE Cybersecurity Report 2024 that you can Access Here – UAE Cybersecurity Report 2024