The State of
Cybersecurity in UAE
Download the 2025 Report Today,

Bridging the Gap
Addressing Today's Cybersecurity Challenges: Insights for Your Organization
In an era of increasing cyber threats, understanding your vulnerabilities is crucial. Our report equips you with the knowledge to navigate risks and strengthen your defenses.
Preview
What you'll learn in this report
01 Unequal Ground: Cyber Disparities and Disruptions
Global vs. Regional Readiness
Supply Chain & Ecosystem Vulnerabilities
Geopolitical Tensions & Regulatory Complexities
02 Navigating the Complex World of Cybersecurity
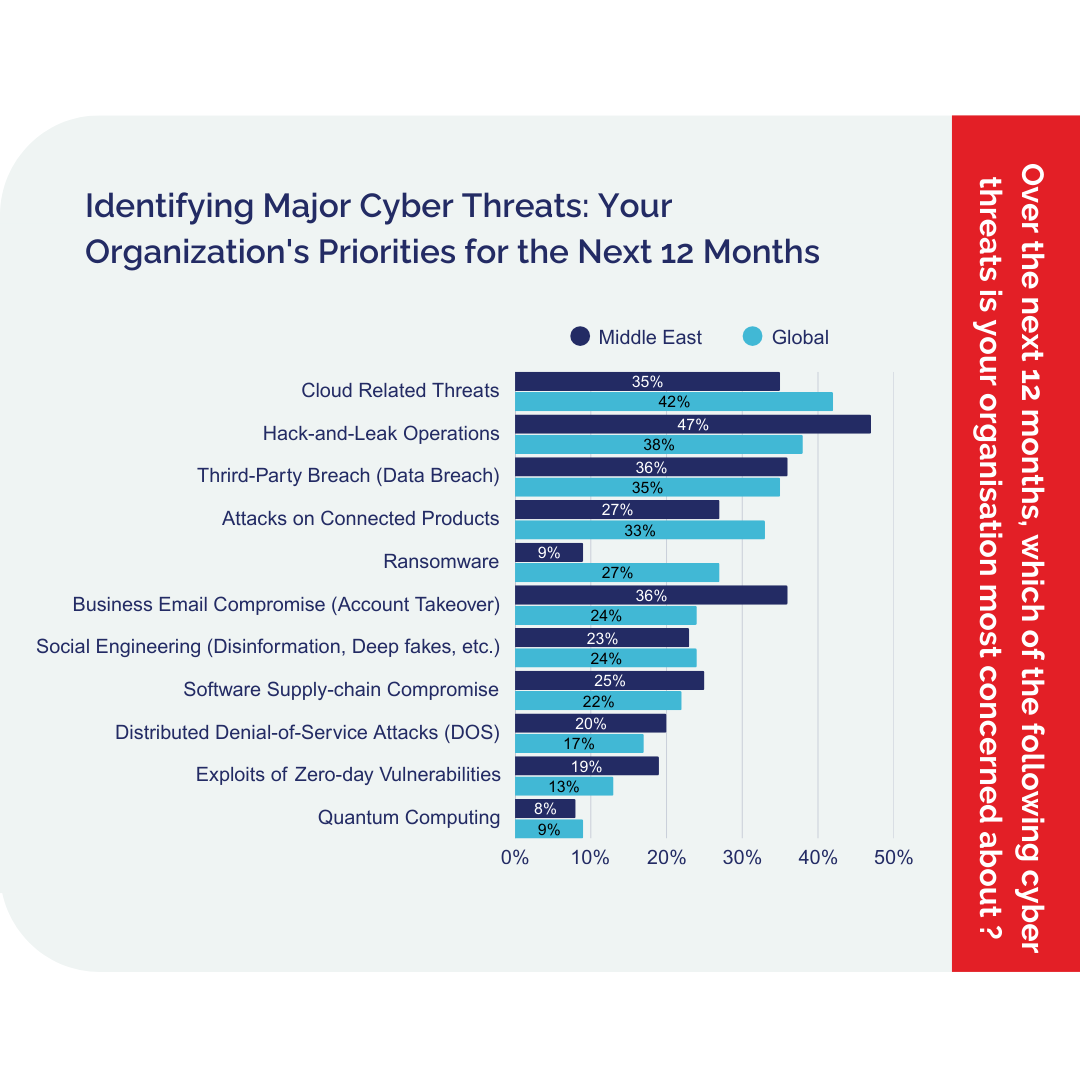
The Evolving Battlefield: Threat Types & Trends
Embracing the Future: AI & Advanced Technologies
Interconnected Risks: Dependencies & Ecosystem Vulnerabilities
Assessing Readiness: Cyber Resilience Maturity
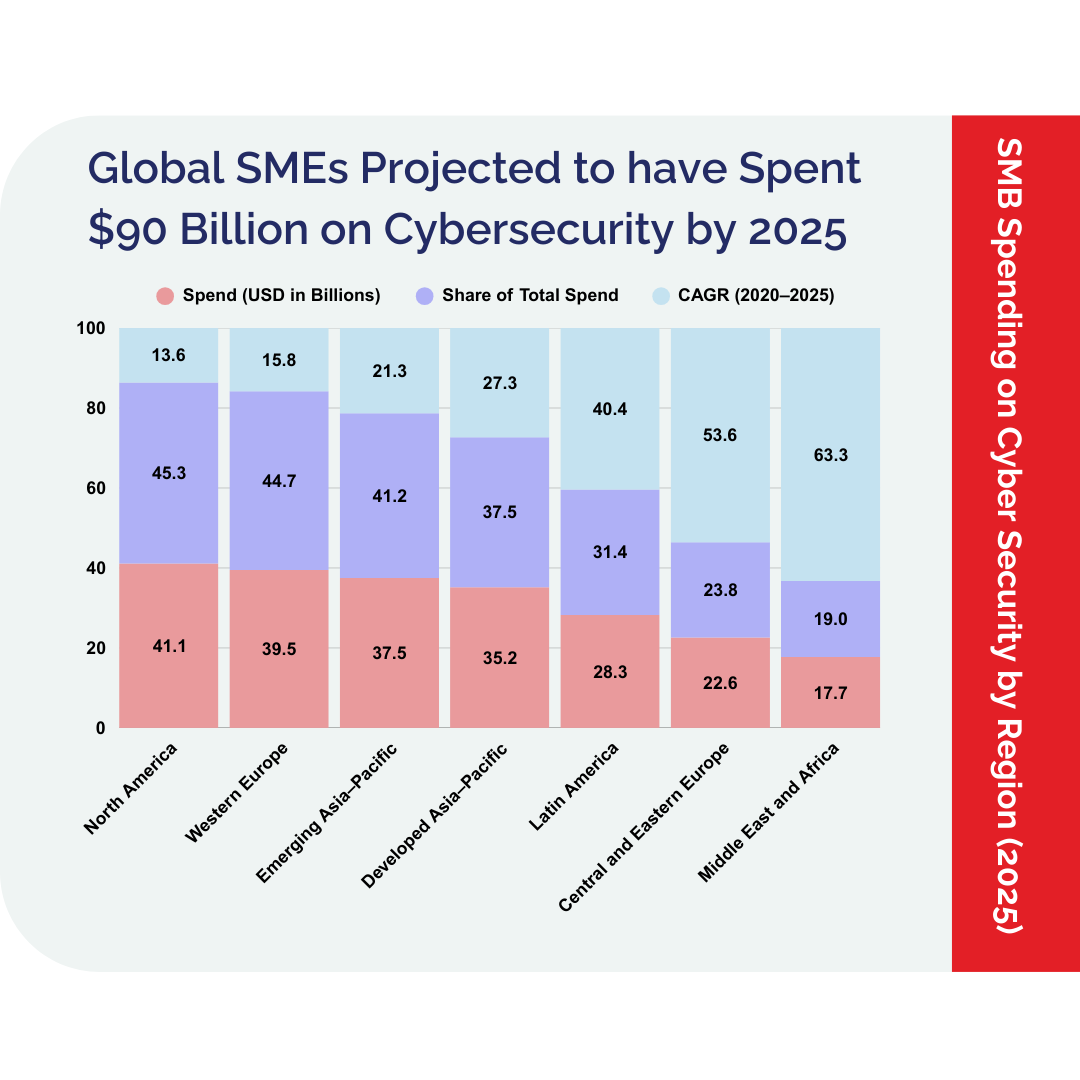
03 The Financial Frontline
Economics of Cyber Defense
Bridging the Cyber Skills Gap
04 The Essential Practices: Cybersecurity Action Plan
20 Critical Best Practices to Implement Immediately
05 Measuring Preparedness: A Cybersecurity Self-Test
Self-Evaluation Questions for IT Leaders
Insights
Demystifying Cyber Security Complexity
The escalating complexity in cyberspace demands a strategic approach to cybersecurity that addresses the economic implications, skill gaps, and practical measures organizations must take to safeguard their digital assets.
Threats Are Getting Smarter, Not Simpler
Discover how AI-powered attacks, ransomware, and identity-based threats are evolving—and why old strategies no longer work.
Your Supply Chain Could Be Your Weakest Link
Learn why small vendors in your ecosystem may be exposing you to large-scale breaches—and what top organizations are doing to manage third-party risk.
Visibility Is Power in 2025
Get a framework for consolidating tools, reducing complexity, and boosting your cyber resilience through smarter architecture and AI-led insights.
AI Is a Double-Edged Sword
The report reveals how AI can slash response times from days to minutes—but also introduces new risks when poorly managed.
Too Many Rules, Too Little Clarity
With overlapping global and regional regulations, even the most compliant companies struggle to keep up. This report simplifies what really matters for your business.
The Talent Shortage Is Now a Cyber Risk
With 66% of companies facing critical skills gaps, the report offers strategies to fill the void—without waiting for the perfect hire.
Unlock Latest Cybersecurity Insights
Gain exclusive access to the State of Cybersecurity in the UAE – 2025 Report—your essential guide to navigating the evolving digital threat landscape.
Peek Into the Magic We Create






Cyber Threat Intelligence
Brand Threat Monitoring
Attack Surface Monitoring
Dark & Deep Web Monitoring
Data Leaks Monitoring
Infrastructure Monitoring
Real-time application threat mitigation
Updated reputation data daily
Protection against the OWASP Top 10 Attacks
API Discovery & Risk Assessment
API Security Posture
Runtime Protection
Secure API Deployment
API Security Insights
Security Data Lake for Threat Hunting
Bot Mitigation & Fraud Detection
Cyber Threat Intelligence
Security Control Validation
Attack Path Validation
Detection Rule Validation
Attack Surface Validation
Cloud Security Validation
Discovery
Analysis
Validation
Exploitation
Reporting
Network Infrastructure Testing
Web Application Testing
Cloud Penetration Testing
Wireless Testing
Social Engineering
Mobile Security
OT Security
Cyber Risk Assessment
Risk Treatment Plan
Technology Implementations
Policies & Procedures
Implementation Reviews
Security Testing
Security Awareness
Internal Audits
Perimeter & Content Security
Firewall & UTM
Endpoint Security
Business Intelligence Analytics
Ransomware Susceptibility Checks